Cyber Protection
Free Vector Cyber Security Flyer Square

Cybersecurity In Europe Stronger Rules And Better Protection Consilium
30 Cyber Security Awareness Tips Your Business Needs

Comparing Top 11 Cyber Protection Solutions For Businesses

Premium Vector Cyber Security Instagram Posts

Telefonica Backs Nozomi In Latest Cybersecurity Move Mobile World Live
Cyber Security Readiness Small to midsized businesses often lack the resources to keep up with new cyber threats Strengthen your operational security posture with an assessment and an actionable plan to improve upon your strengths and address your vulnerabilities.

Cyber protection. Cyber attacks are a growing concern for small businesses Learn about the threats and how to protect yourself. Cybersecurity Biden poised to pick Obamaera security veterans for 3 top cyber roles The leading candidates for the cyber positions have been described as well prepared to confront an ongoing. Cyber personal protection Covers breaches of privacy, cyber bullying and cyber disruption, the latter referring to events that prevent you from accessing your home or interrupting a small business you run from your home.
CYBERSECURITY CISA leads the Nation’s strategic and unified work to strengthen the security, resilience, and workforce of the cyber ecosystem to protect critical services and American way of life. Cyber Protection, which protects your business against damage caused by a virus or computer attack, as well as helping with the cost of restoring and recreating data We also offer tips to help you manage your computer and technology risks resulting from data loss, data breaches, denial of service attacks, malware, viruses and more. Cyber security refers to the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access Cyber security may also be referred to as information technology security The Importance of Cyber Security.
Cyber Protection, which protects your business against damage caused by a virus or computer attack, as well as helping with the cost of restoring and recreating data We also offer tips to help you manage your computer and technology risks resulting from data loss, data breaches, denial of service attacks, malware, viruses and more. Although cyber insurance is a growing market, standalone personal cyber insurance policies have yet to gain traction The most prominent insurer to offer comprehensive cyber protection is State Farm, with its Cyber Event, Identity Restoration and Fraud Loss coverage This coverage can be purchased as an addon to State Farm home insurance. Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access In a computing context.
The IP behind Covid19 vaccines and their supporting supply chains need stateoftheart protection comprised of cybersecurity technologies and systems, as the vaccines' IP is an asset that cyber. The IP behind Covid19 vaccines and their supporting supply chains need stateoftheart protection comprised of cybersecurity technologies and systems, as the vaccines' IP is an asset that cyber. One Subscription & Unlimited Device Protection From Internet Threats at Home and OnTheGo NETGEAR Armor is multilayer cybersecurity with subscriptions starting at $9999 $6999 and is available exclusively on Orbi Mesh WiFi Systems and Nighthawk Routers.
Cyber protection ensures that access, while balancing it against the need to keep digital environments and assets safe, private, authentic, and secure Locking a hard drive in a vault makes the contents safe but inaccessible – so it’s not useful. Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information;. Philadelphia Insurance Companies' Cyber Security Liability program provides both First and Third Party coverage for numerous classes of business Through eight Insuring Agreements, a wide range of cyber liability exposures are addressed Coverage is available nationwide on either an admitted or nonadmitted basis.
Or interrupting normal business processes. Protect an unlimited number of smart devices* from cyber threats with a single subscription NETGEAR Armor™ provides multilayered cybersecurity on your smartphones, computers, smart TVs, security cameras, and anything else connected in your home. Extorting money from users;.
Definition Cyber security or information technology security are the techniques of protecting computers, networks, programs and data from unauthorized access or attacks that are aimed for exploitation Description Major areas covered in cyber security are 1) Application Security 2) Information Security 3) Disaster recovery 4) Network Security. Cybersecurity Biden poised to pick Obamaera security veterans for 3 top cyber roles The leading candidates for the cyber positions have been described as well prepared to confront an ongoing. Cybersecurity The CISA Insights Risk Management for Novel Coronavirus (COVID19) provides executives a tool to help them think through physical, supply chain, and cybersecurity issues that may arise from the spread of COVID19 On March 6, CISA released an alert reminding individuals to remain vigilant for scams related to COVID19 Cyber actors may send emails with malicious attachments or links to fraudulent websites to trick victims into revealing sensitive information or donating.
Supplier Cyber Protection Service This service allows the Ministry of Defence (MOD) and industry partners to manage cyber risk across the defence supply chain Published 2 October 17. The National Cybersecurity Protection System (NCPS) is an integrated systemofsystems that delivers a range of capabilities, such as intrusion detection, analytics, information sharing, and intrusion prevention These capabilities provide a technological foundation that enables the Cybersecurity and Infrastructure Security Agency (CISA) to secure and defend the Federal Civilian Executive Branch (FCEB) agencies' information technology infrastructure against advanced cyber threats. One way to start this process is to take advantage of the Department of Homeland Security’s Industrial Control Systems Cyber Emergency Response Team (ICSCERT) ICSCERT provides a wide range of information, tools, and services that can help companies assess their security, identify recommended practices, and improve their cyber security http//icscertuscertgov/.
Predict Adapt Synchronize Advanced Endpoint Protection and Network Security Fully Synchronized in Real Time Sophos is Cybersecurity Evolved. Cyber security is the state or process of protecting and recovering networks, devices and programs from any type of cyberattack Cyberattacks are an evolving danger to organizations, employees and consumers They may be designed to access or destroy sensitive data or extort money. Predict Adapt Synchronize Advanced Endpoint Protection and Network Security Fully Synchronized in Real Time Sophos is Cybersecurity Evolved.
Make it safer for your business to innovate As one of the world’s largest Managed Security Services Providers (MSSP), AT&T Cybersecurity delivers the ability to help safeguard digital assets, act with confidence to detect cyber threats to mitigate business impact, and drive efficiency into cybersecurity operations. Cyber Security is a set of techniques that are used to protect the internetconnected systems It can protect computers, networks, software, and data Cyberattacks are performed to make unauthorized access, change or destroy data, or to extort the money. Definition Cyber security or information technology security are the techniques of protecting computers, networks, programs and data from unauthorized access or attacks that are aimed for exploitation Description Major areas covered in cyber security are 1) Application Security 2) Information Security 3) Disaster recovery 4) Network Security Application security encompasses measures or.
Turn challenges into opportunities Stay ahead of modern threats Spend more time focused on your overall security posture, rather than on managing the Gain proactive cyber protection Avoid downtime, prevent loss of employee productivity, and spend less time on costly Eliminate unnecessary. As the nation's risk advisor, the Cybersecurity and Infrastructure Security Agency (CISA) brings our partners in industry and the full power of the federal government together to improve American cyber and infrastructure security Since the beginning of the Coronavirus threat, also known as COVID19, CISA has been monitoring the evolving virus. Cyber insurance is a subcategory of general insurance that covers businesses and individuals against internetbased liability and risks There are generally two levels of cyber liability coverage.
Make it safer for your business to innovate As one of the world’s largest Managed Security Services Providers (MSSP), AT&T Cybersecurity delivers the ability to help safeguard digital assets, act with confidence to detect cyber threats to mitigate business impact, and drive efficiency into cybersecurity operations. Make it safer for your business to innovate As one of the world’s largest Managed Security Services Providers (MSSP), AT&T Cybersecurity delivers the ability to help safeguard digital assets, act with confidence to detect cyber threats to mitigate business impact, and drive efficiency into cybersecurity operations. To help families and volunteers keep youth safe while online, the Boy Scouts of America introduces the Cyber Chip In developing this exciting new tool, the BSA teamed up with content expert NetSmartz®, part of the National Center for Missing and Exploited Children® and training expert for many law enforcement agencies.
Malicious cyber activity threatens the public’s safety and our national and economic security The FBI’s cyber strategy is to impose risk and consequences on cyber adversaries Our goal is to. Cybersecurity Biden poised to pick Obamaera security veterans for 3 top cyber roles The leading candidates for the cyber positions have been described as well prepared to confront an ongoing. Cyberattacks are a serious economic and security threat To combat both immediate and future dangers, businesses and governments are investing in cyber security Understanding trends in cybersecurity and how machinelearning techniques defenses can respond to threats is a critical component of protecting networks, infrastructure and users.
Cyber Security Strategies Besides understanding cyber law, organizations must build cybersecurity strategies Cybersecurity strategies must cover the following areas Ecosystem A strong ecosystem helps prevent cybercrime Your ecosystem includes three areas—automation, interoperability, and authentication. Although cyber insurance is a growing market, standalone personal cyber insurance policies have yet to gain traction The most prominent insurer to offer comprehensive cyber protection is State Farm, with its Cyber Event, Identity Restoration and Fraud Loss coverage This coverage can be purchased as an addon to State Farm home insurance. Securing cyberspace is a 24/7 responsibility, and every individual is the first line of defense For resources to help keep personal and professional online experiences safe, visit our fact sheets.
Cybersecurity standards are techniques generally set forth in published materials that attempt to protect the cyber environment of a user or organization This environment includes users themselves, networks, devices, all software, processes, information in storage or transit, applications, services, and systems that can be connected directly or indirectly to networks The principal objective is to reduce the risks, including prevention or mitigation of cyberattacks These published materials c. Cyber threats are everywhere, and they affect everyone More than 60% of Americans have personally experienced a major data breach (Pew Research Center) The cost of the average data breach to a US company was nearly $8 million (Symantec 19 Internet Security Threat Report). How to protect yourself against cybercrime 1 Use a fullservice internet security suite For instance, Norton Security provides realtime protection against 2 Use strong passwords Don’t repeat your passwords on different sites, and change your passwords regularly Make them 3 Keep your.
Discuss cyber security with those organizations and consider incorporating good cyber practices into marketing and contracting • Measure Your Progress – Test your cyber practices through drills and exercises Identify any gaps or lessons learned, and set specific goals with timelines for making needed improvements. Biden intends to nominate Rob Silvers, who was the Obama administration's assistant secretary for cyber policy at the Department of Homeland Security, to fill Krebs' role, Reuters reported. Cyber Security is National Security Home » Cyber Security is National Security After the President released the National Cyber Strategy in 17, Energy Secretary Brouillette clearly stated, “Advancing cybersecurity is a core priority for the Department of Energy”.
This is why DOE is committed to working with the private sector to increase cyber security and resiliency in the prevention of cyberattacks In 18, Secretary Brouillette signed and endorsed the Cybersecurity Strategy of 10, a strategy that outlines the vision to secure the Department of Energy. Security controls between each level are typified by a “demilitarized zone” (DMZ) and a firewall Conventional approaches restrict downward access to Level 3 from Levels 4, 5 (and the internet) Heading upward, only Layer 2 or 3 can communicate with Layers 4 and 5, and the lowest two Levels (machinery and process) must keep their data and. Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access In a computing context.
The US Army Cyber Protection Brigade (CPB), the first of its kind in the Army, was activated at its home station at Fort Gordon, Georgia, on Sept 5, 14 The CPB's mission is to defend key.

Threat Protection And Cyber Security Recruitment Jonathan Lee
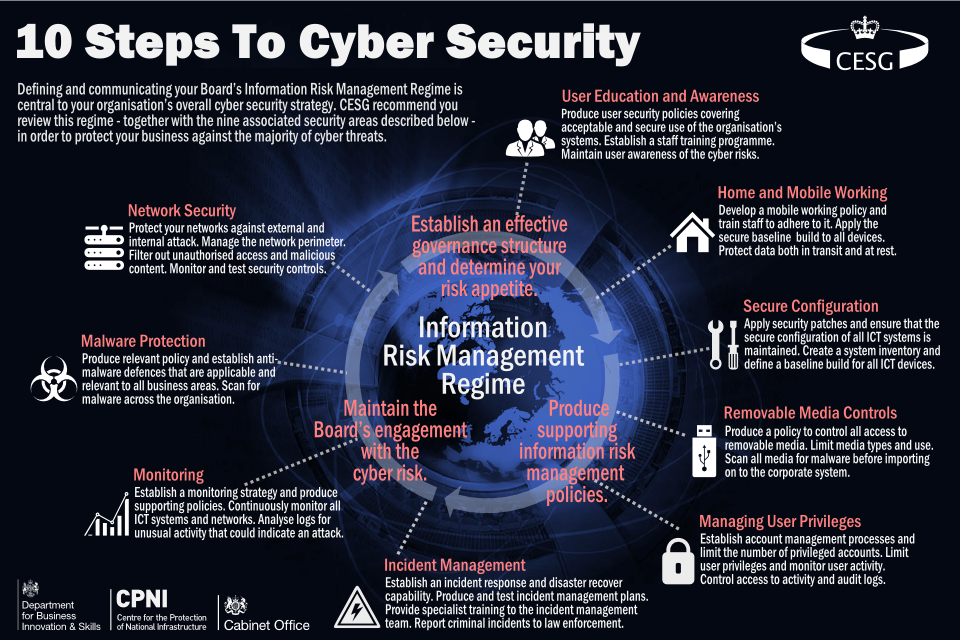
Withdrawn 10 Steps Summary Gov Uk

Cyber Protection Full Range Of Cyber Protection Solutions Acronis

Acronis Delivers Cyber Protection Where Data Protection And Cybersecurity Merge Youtube

Covid 19 Is Accelerating The Digital Transformation Of Cyber Security

5 Essential Cyber Security Themes Fermanagh Enterprise Limited

Threat Protection Choosing A Cyber Security Partner

Acronis Acquires Cyberlynx Enhances Cyber Protection Portfolio With Additional Security Services Financial It

Taking Responsibility For Cyber Security In A Truly Virtual World

W Series And Acronis Announce Cyber Protection And Security Partnership Motorsport Technology

Global Open Standards For Cyber Security Beyond Standards

Future Cyber Security Protection Reflection From The Ups And Downs Of Covid 19 1 Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks

How To Practice Cybersecurity And Why It S Different From It Security Cso Online

The Human Side Of Cyber Security From Threat To Defender Ibm Big Data Analytics Hub
What Is Cyber Security Definition Best Practices

Acronis Cyber Protect Cloud World S First Complete Cyber Protection Solution In The Remote Work Era Znetlive Blog A Guide To Domains Web Hosting Cloud Computing

Steamship Mutual Cyber Security And Data Protection

Master Of Science In Security Studies Cybersecurity Concentration Online Criminal Justice Security Studies Major Umass Lowell
Q Tbn And9gctcqug93ztsenn3uzr2dvi169pik Lrcrm Hwxp Fuityq4x0q Usqp Cau

What Is Cyber Security Definition Types And User Protection Kaspersky

Us Citizens Want Government To Strengthen Cyber Protection Smart Cities World

Guest Blog Data S Value To Businesses Demands The New Approach Of Cyber Protection Acronis Blog

Cybersecurity Talent The Big Gap In Cyber Protection

Cyber Security Data Protection And Privacy Abla

Small Business Cyber Security An Essential Guide

Full Recording An Enlightened Approach To Cyber Protection Friedman Llp

Tac Cyber Protection

The Top 25 Cybersecurity Companies Of 19 The Software Report

Best Cybersecurity Website Protect Your Site With Cwatch Security

The Five Ways To Ensure Cyber Security This Christmas

Cyber Security Solutions Cyber Security Protection Services
3

Assured Cyber Protection Acp Linkedin
Q Tbn And9gcsa6tz Vdol3rw13hqpzmyfhyx G3f2tl Qituymya Usqp Cau

Grid Security Energy Automation And Smart Grid Siemens Global

World Cyber Protection Week Survey Reveals Most It Pros Back Up Their Data But Still Can T Sleep At Night Acronis Blog

Cyber Security What Think Tanks Are Thinking European Parliamentary Research Service Blog

How To Land The Best Jobs In Cyber Security Includes Salary Data

Top 11 Most Powerful Cybersecurity Software Tools In 21

Cybersecurity Emerson Us

Convergint Is Offering A Free Trial Of Cyber Protection Plus For 45 Days Convergint

What S The Difference Between Cyber Security And Information Security By Michael Warne Medium

Cyber Security For Fire Protection Systems Ul

The Three Pillar Approach To Cyber Security Data And Information Protection Dnv Gl
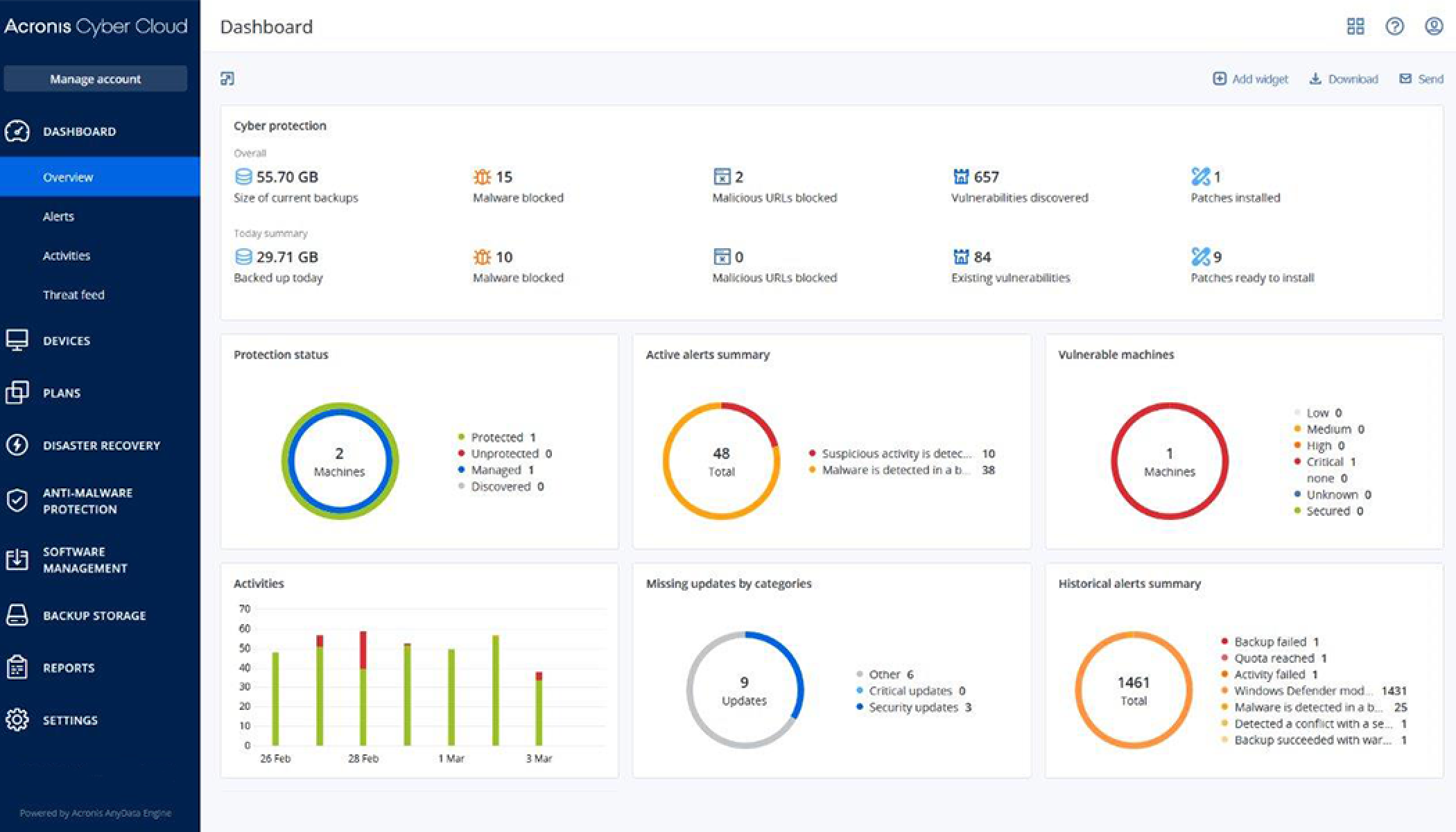
Singapore Unicorn Acronis Released The World S First Complete Cyber Protection Solution Tailored To Fight Pandemic Cyberthreats And Improve Remote Work

Strong Leadership Is A Company S Best Cyber Protection Lloyd S List

Critical Information Systems And Cybersecurity Thales Group

What Is Cyber Security Definition Best Practices More Digital Guardian

How To Protect Your Practice From Cyber Attacks With Cyber Security

71 231 Cyber Security Illustrations Royalty Free Vector Graphics Clip Art Istock

Cyber Security Threats In The Food Beverage Industry Sobelco

Cyber Protection Services Linkedin

Cyber Security And Data Protection

Itwire Acronis Cyber Protect 15 Total Cyber Protection Needed As 31 Of Companies Face Cyber Attacks Daily

Taking Advantage Of Ai In Cyber Security Strategies Cyber Security Hub
%20FINAL.jpg?width=993&height=2423&name=6%20point%20cyber%20security%20checklist%20vertical%20version%20(4D)%20FINAL.jpg)
Infographic Cyber Security Checklist For 19

Reason For Using Artificial Intelligence In Cyber Security Cyberdb

Cyber Security Job Types Careersincyber Com

Modern Cyber Protection 5 Vectors You Need To Know Znetlive Blog A Guide To Domains Web Hosting Cloud Computing

How Ai Ml And Automation Can Improve Cybersecurity Protection Techrepublic

Grow Your Msp Or Var Business With Cyber Protection Services Channel Futures

Imo 21 Puts A Spotlight On Cyber Security Marine Offshore

A Moment Of Reckoning The Need For A Strong And Global Cybersecurity Response Microsoft On The Issues

Maintaining Your Mission The Need For Complete Cyber Protectionwebinar

Cyber Security Protection 7 Steps Ship Operators Can Take Now Shipinsight

Cybersecurity Solutions Atos

Cyber Security Omicron

Business Man On Laptop Cyber Security Banner Download Free Vectors Clipart Graphics Vector Art

Comarch Cyber Security Software Solution Find Out More

Cyber Security

Awareness Is Key To Aviation Cyber Protection Embry Riddle Aeronautical University Newsroom

Brexit The Implications For Cyber Security And Data Protection Institute Of Directors Iod

Latest Maritime Cyber Security And Threats Safety4sea

Axa Xl Accenture Partner To Provide Cyber Security Services To Axa Xl Clients

Pa Business One Stop Shop Cyber Security And Privacy Protection In The Time Of Pandemic

These Cyber Protection Tips Can Help Keep Your Business Safe Personal Insurance Business Insurance Cd G Insurance In Oakland

Importance Of Cyber Security Protection For Australian Businesses

Top 15 Tips To Improve Cyber Security Telappliant

Pensions And Cyber Security Is The Industry Addressing The Risks Fieldfisher

Government And Water Industry Warned Of Cyber Security Blind Spots International Water Power

Assured Cyber Protection Acp Technology Twitter

Why Businesses Must Make Cyber Security Skills A Priority In 17 Information Age
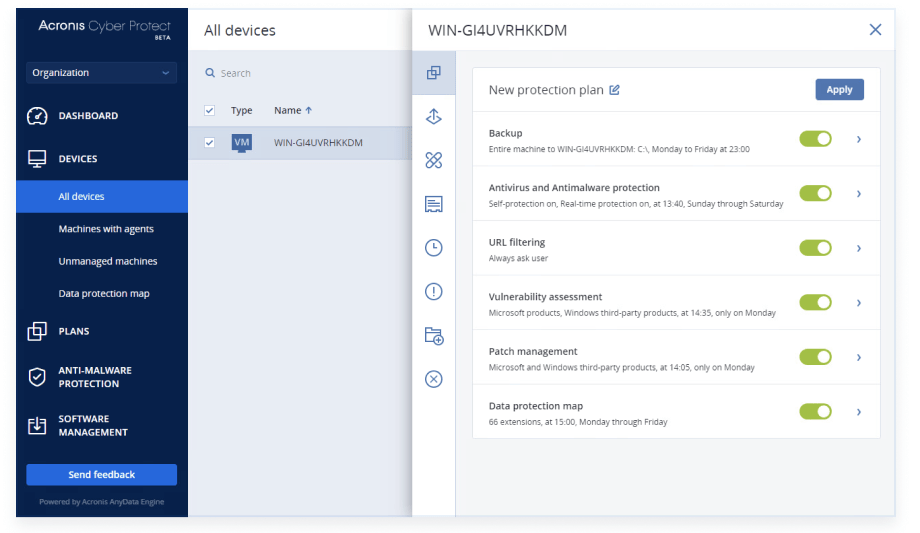
Acronis Launches Cyber Protect 15 Cybersecurity Solution Security News Sourcesecurity Com

How To Protect Your Small Business From Cyber Attacks Bytestart

Cybersecurity Universita Di Padova

Why Is Cyber Security Important It Company Birmingham

5 Cyber Security Trends In Businesses Need To Know Mybusiness

Acronis Makes Remote Work Environments More Secure Launches Acronis Cyber Protect

Cyber Security Courses Study Online With Top Universities Futurelearn

Cyber Security Strategy And Response Fieldfisher

What Are The Types Of Cyber Security Vulnerabilities Logsign
.jpg)
Nas Announces New Cyber Protection For High Net Worth Individuals Insurance Business

Royal Navy Brings Cyber Protection Into The Spotlight Safety4sea

Cybersecurity Information Protection At Ccm Cyber Security Information Protection

Cyber Security Wdigital

Understanding Modern Cyber Protection What You Need To Know Acronis Blog

G27dbizeaszrcm



