From A To Z Projective Coordinates Leakage In The Wild

Pdf From A To Z Projective Coordinates Leakage In The Wild Semantic Scholar
2
Cryptojedi Org Papers Ota Pdf

M8ta Fun

Pdf From A To Z Projective Coordinates Leakage In The Wild Semantic Scholar

State Of The Environment Of The Black Sea 09 14 5
The construction of Z is slightly involved, but on a high level, Z internally simulates the actions of Z~ including all ITIs activated by Z~ (other than those for G and the lth instance of ˇ), but forwards all communications sent to the lth instance of ˇto its own external interaction.
From a to z projective coordinates leakage in the wild. In this case the exact WKB analysis leads to consideration of a new sort of Darboux coordinate system on a moduli space of flat \({\mathrm {SL}}(3)\)connections We give the simplest example of such a coordinate system, and verify numerically that in these coordinates the monodromy of the \(T_3\) equation has the expected asymptotic properties. From A to Z Projective coordinates leakage in the wild 📺 Abstract Alejandro Cabrera Aldaya Cesar Pereida García Billy Bob Brumley At EUROCRYPT 04, Naccache et al showed that the projective coordinates representation of the resulting point of an elliptic curve scalar multiplication potentially allows to recover some bits of the scalar. Projective Coordinates Leak May 04;.
813 Likes, 2 Comments UWMilwaukee (@uwmilwaukee) on Instagram “Happy #PantherPrideFriday 🐾💛 us in your photos to be featured on our page or in our Photos of”. I ∈ I We call CIS (unrestricted) code a systematic code which admits two complementary information sets The Hamming weight w(z)of a binary vector z is the number of its nonzero entries The weight enumerator WC(x,y)of a code C is the homogeneous polynomial defined by WC(x,y)= X. Aschwanden et al 03;.
In exactly one codeword within the specified coordinates xi;. In appropriate projective coordinates the Hesse pencil is given by the equation (1) λ (x 3 y 3 z 3) μxyz = 0 The pencil was classically known as the syzygetic pencil 2 of cubic curves (see 9, p 230 or 16, p 274), the name attributed to L Cremona. Abstract Synchronous bursting (SB) is ubiquitous in neuronal networks and independent of network structure Although it is known to be driven by glutamatergic.
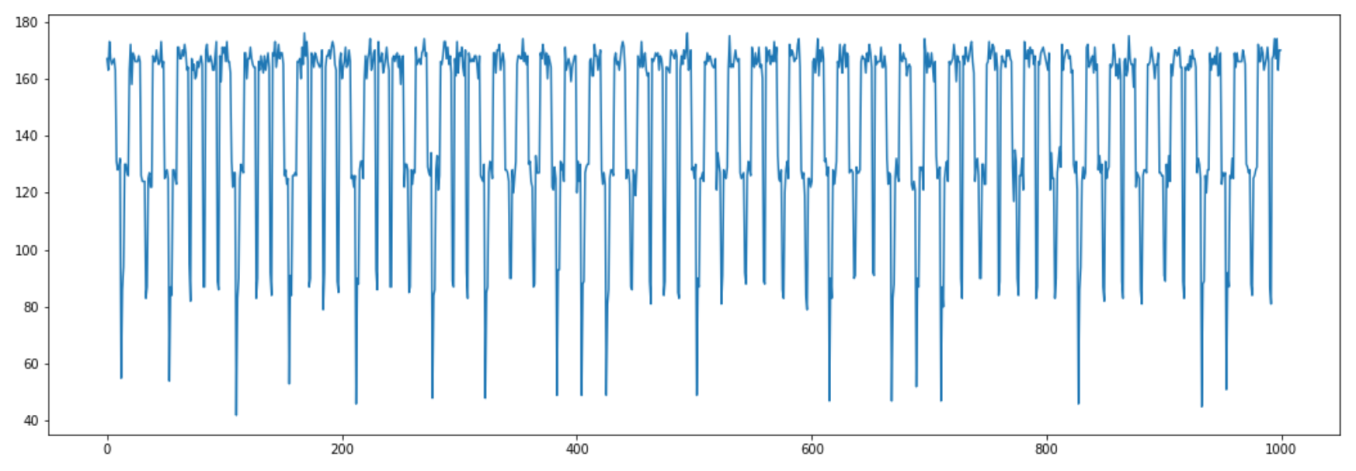
So leakage of coordinates of the NTT transform is a natural model for key exposure attacks NewHope key exchange protocol Some of our results focus on analysis of the NewHope key exchange protocol of 4 in the presence of partial key exposure Brie. In certain embodiments, to eliminate DC leakage into surrounding AC values, scaling stage within a photo overlap transform operator is modified such that the offdiagonal elements of the associated scaling matrix have the values of 0 In certain embodiments, the ondiagonal scaling matrix are given the values (05, 2) In some embodiments, the scaling is performed using a combination of. For example, from the model data in Figure 15a, for Z = 01 and N D = 4, a % decrease in path length can lead to a 5‰ decrease in vein δ 18 O However, above the isotopic front, for example at Z = 06, a % decrease in reactive path length decreases vein δ 18 O by less than 1‰.
Also we deduce that a mapping f ∈ H(B) has parametric representation if and only if there exists a Loewner chain f(z,t) such that the family {et f(z, t)} t ≥ 0 is a normal family on B and f(z) = f(z,0) for z ∈ B Finally we conclude that the set S 0 (B) of mappings which have parametric representation on B is compact. WT, wild type Cell death was quantified by a leaf disk ion leakage (conductivity) assay at 3 days after agroinfiltration (dai) Data are normalized to the mean value for samples with RPP1_WsB and WT ATR1_Emoy2 in each experiment. Emergency evacuations are more common than many people realize, including evacuations in the workplace According to the US Department of Homeland Security (DHS) Federal Emergency Management Agency (FEMA), the most frequent causes of evacuations in the US each year are fires and floods In.
Izi 2Z pz can be computed with O(nlogn) operations by FFT interpolation We will use the following Lemma while proving correctness of coefficients of a polynomial Lemma 2 (Schwartz–Zippel) Let pz;qz be two ddegree polynomials from Z pz Then for w $ Z p, the probability that p(w)=z(w) is at most d=p, and the equality can be tested. Since the only preferred direction in the system is the zdirection, the coordinate system can be rotated such that k y = 0 (without loss of generality), then In what follows, we drop the subscript "x" and use k instead of k x The linearized MHD equations take the form of three equations for the variables v x, v y, and v z, respectively. Tampere University Defeating StateoftheArt WhiteBox Countermeasures with Advanced GrayBox Attacks.
We present the geomagnetic field model COVOBSx1, covering 1840 to , from which have been derived candidate models for the IGRF12 Towards the most recent epochs, it is primarily constrained by first differences of observatory annual means and measurements from the Oersted, Champ, and Swarm satellite missions Stochastic information derived from the temporal spectra of geomagnetic series. Three‐dimensional visualization of the Earth's magnetic field topology in GSM coordinates computed using T96 model (Tsyganenko, 1996) at 924 UT in the x‐z plane (a) and in the y‐z plane (b), respectively The MMS orbit between 8 and 1100 and location between 0924 are shown in red line and by a (magnified) black circle, respectively. The con from holes Z9K and Z1062 bored into room 305/2 235 236 tribution made to the total αactivity by U and U and was taken in the southern part of room 012/8 –3 is lower than that made by U by a factor of 15 and 3, (sampling point 35) is within 021–10 mg dm respectively.
In , a Z / p Zcovering of an affine variety Spec A is investigated, and it is shown that if A is a noetherian factorial domain satisfying the condition that every projective Amodule of rank p, p − 1, p − 2 is free then every Z / p Zcovering of Spec A is given as Spec B, where B = A z / (z p − z − a) with a ∈ A. Tum cohomology of the projective space (Iritani also showed that this can be extended to the quantum cohomology of Fano toric varieties or orbifolds) This is strongly related to the notion of TERP structure of Hertling 1 Tame versus wild in complex analytic geometry dimension one • ∆ disc, coord z • ∆ =e S1 ×0,1) real blowup. We developed a threedimensional numerical model of LargeModeArea chirped pulse fiber amplifiers which includes nonlinear beam propagation in nonuniform multimode waveguides as well as gain spectrum dynamics in quasithreelevel active ions We used our model in tapered Ybdoped fiber amplifiers and showed that singlemode propagation is maintained along the taper even in the presence of.
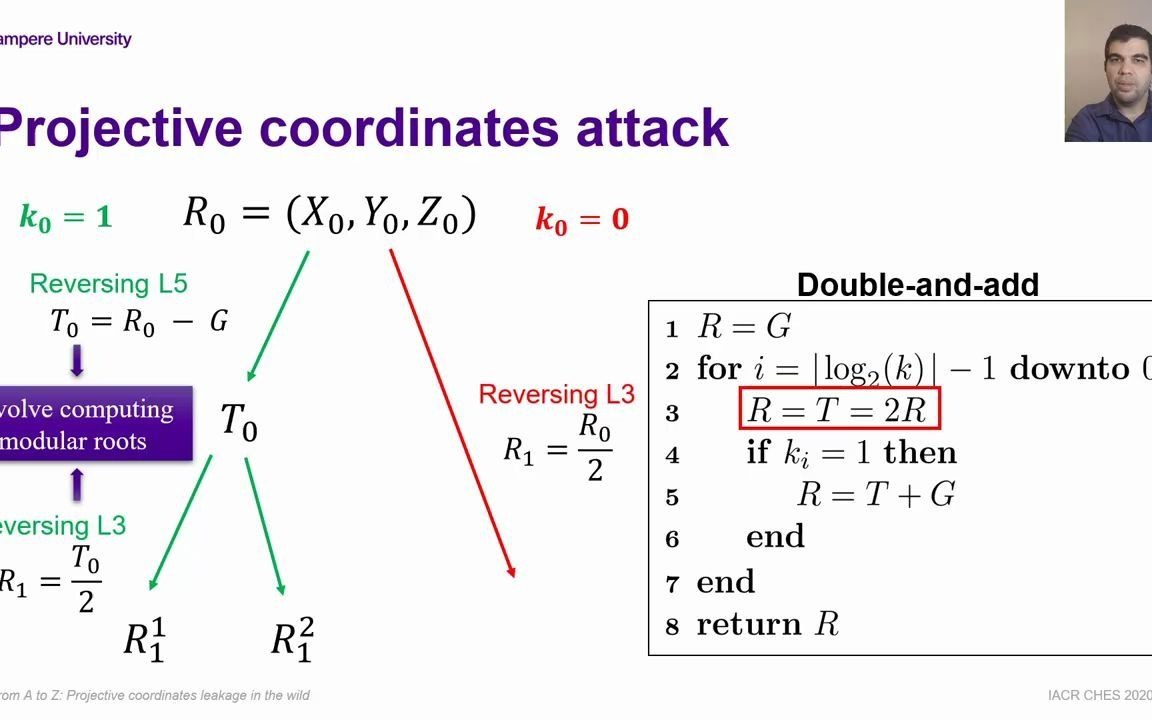
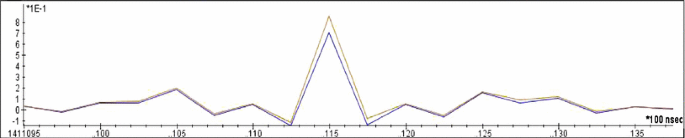
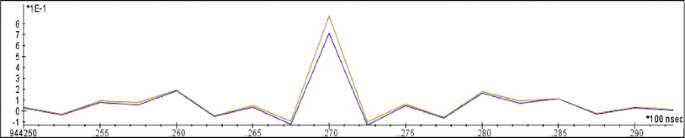
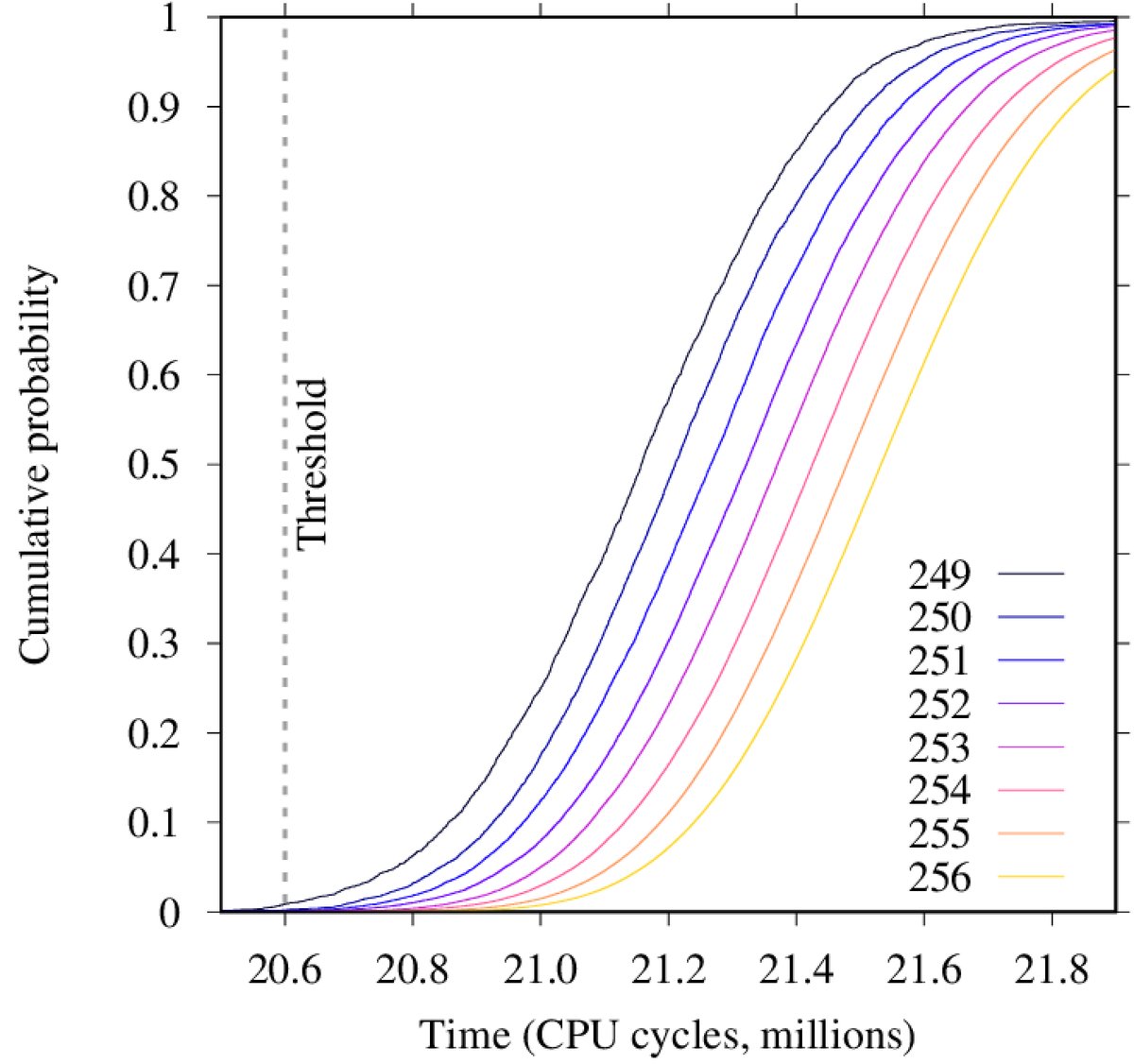
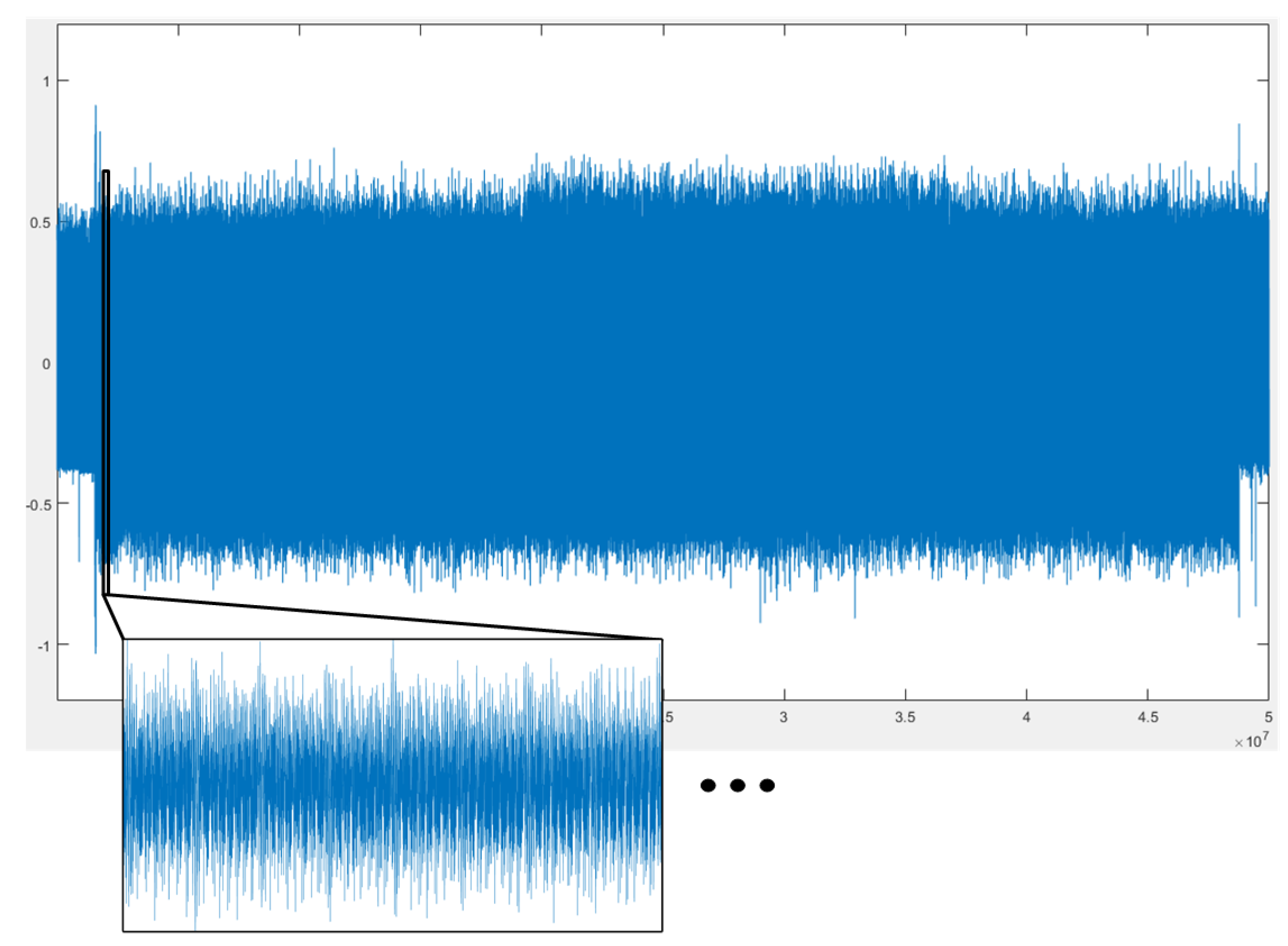
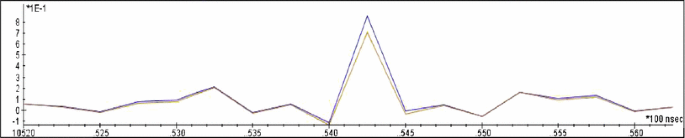
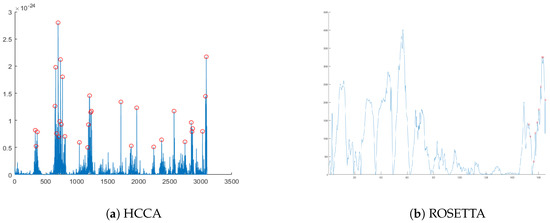
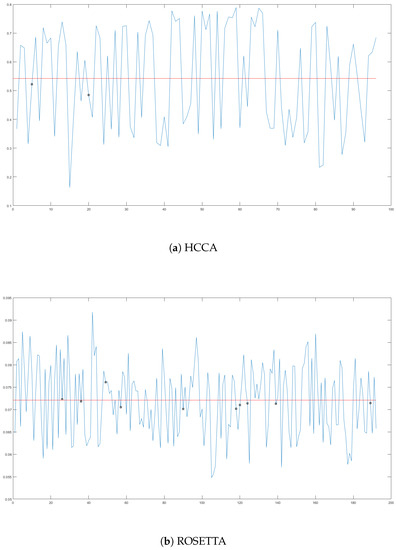
The leakage sources available to the attackers depend on the computing platform libgcrypt a projective coordinates attack, singletrace ECDSA nonce recovery, and recoveryofacountermeasuremask The paper is organized as followsSection 2presents background on elliptic curve. Luo et al 04), loop curvature. Add open access links from to the list of external document links (if available) load links from unpaywallorg Privacy notice By enabling the option above, your.
From A to Z Projective coordinates leakage in the wild Alejandro Cabrera Aldaya;. In , a Z / p Zcovering of an affine variety Spec A is investigated, and it is shown that if A is a noetherian factorial domain satisfying the condition that every projective Amodule of rank p, p − 1, p − 2 is free then every Z / p Zcovering of Spec A is given as Spec B, where B = A z / (z p − z − a) with a ∈ A. Leakage in very faint galaxies at z ˘2 4 In this paper we present the detection of LyC photons in the afterglow spectrum of GRBB at z = We further investigate LyC emission in LGRB afterglow spectra, also adding to this case GRBs and A (z = and z = , respectively), the only two previously known GRBs.
R/pokemon r/pokemon is an unofficial Pokémon fan community This is the place for most things Pokémon on Reddit—TV shows, video games, toys. This dipole is meant to model leakage through a coaxial cable The halfwave dipole antenna was simulated using HFSS at a frequency of 1 GHz The length of a halfwave dipole antenna should be equal to λ/2, where λ is the operating wavelength Therefore, to Cartesian coordinates (x,y,z) Eq 1 was used for this purpose. Page 1 advanced quadrature sets, acceleration and preconditioning techniques for the discrete ordinates method in parallel computi ng environments by gianluca longoni a dissertation presented to the graduate school of the university of flor ida in partial fulfillment of the requirements for the degree of doctor of philosophy university of florida 04.
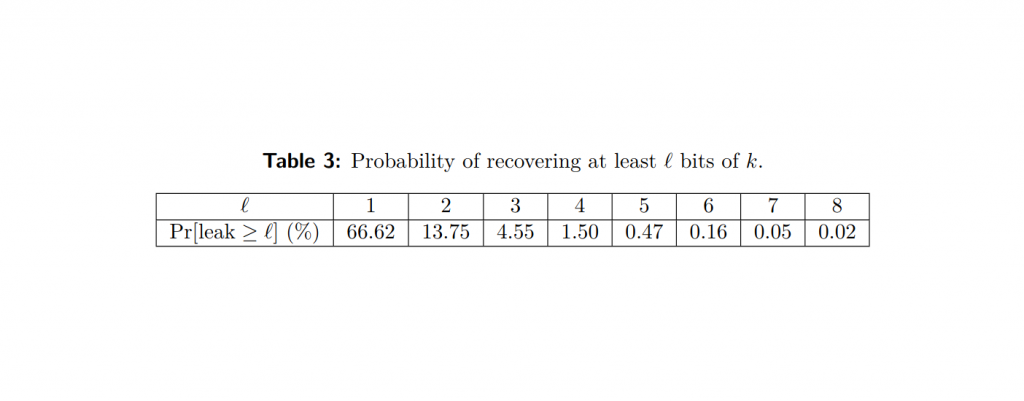
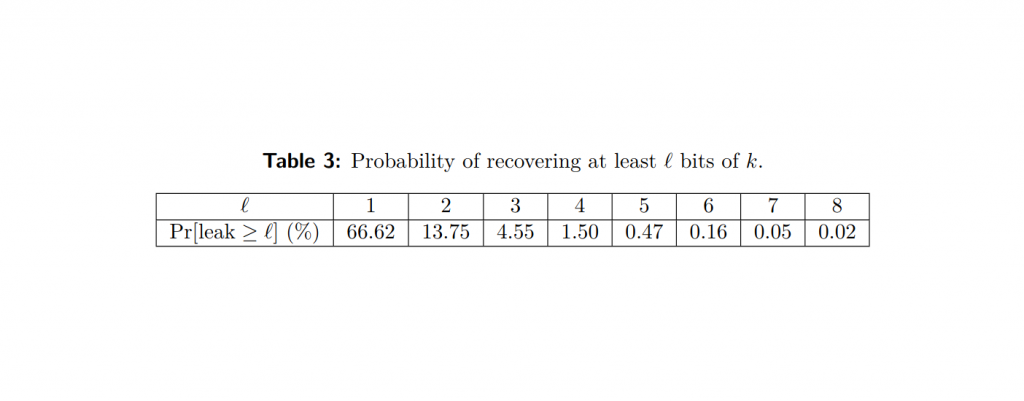
Amplified when multiplied by the LWE secret s, it is essential to assume that s has small coordinates A major part of our reduction (Section 4) is therefore dedicated to showing a reduction from LWE (in dimension n) with arbitrary secret in Zn q to LWE (in dimension nlog 2 q) with a secret chosen uniformly over f0;1g This. Abstract Denoting by P=kG the ellipticcurve doubleandadd multiplication of a public base point G by a secret k, we show that allowing an adversary access to the projective representation of P, obtained using a particular double and add method, may result in information being revealed about k Such access might be granted to an adversary by a poor software implementation that does not. Nonnegligible leakage and the choice of distance measure Nonnegligible leakage Noisy Sum ε = Ω(1/n) for a constant factor approximation to f(x) Leakage is inherent for statistical utility If ε = ο(1/n) for close databases, then ε=ο(1) for two databases ===> no utility Averagecase distance measures.
Izi 2Z pz can be computed with O(nlogn) operations by FFT interpolation We will use the following Lemma while proving correctness of coefficients of a polynomial Lemma 2 (Schwartz–Zippel) Let pz;qz be two ddegree polynomials from Z pz Then for w $ Z p, the probability that p(w)=z(w) is at most d=p, and the equality can be tested. Frontal Attack Leaking ControlFlow in SGX via the CPU Frontend arXivSinglestepping interrupt latency, PTE A/D From A to Z Projective coordinates leakage in the wild CHESPage fault LVI Hijacking Transient Execution through Microarchitectural Load Value Injection S&P link Singlestepping, pagetable manipulation. Also we deduce that a mapping f ∈ H(B) has parametric representation if and only if there exists a Loewner chain f(z,t) such that the family {et f(z, t)} t ≥ 0 is a normal family on B and f(z) = f(z,0) for z ∈ B Finally we conclude that the set S 0 (B) of mappings which have parametric representation on B is compact.
1 Introduction 11 History and background The subject of control is concerned with methods to manipulate the evolution of dynamical systems As such it is relevant to many fields both inside , , , , , and outside , physics Control has a long history, but it emerged as a modern scientific discipline only after the pioneering work of Norbert Wiener in the 1940s. 37 Full PDFs related to this paper READ PAPER Electrical Engineering Handbook. Significance Mitochondria are the energetic, metabolic, redox, and information signaling centers of the cell Substrate pressure, mitochondrial network dynamics, and cristae morphology state are integrated by the protonmotive force Δp or its potential component, ΔΨ, which are attenuated by proton backflux into the matrix, termed uncouplingThe mitochondrial uncoupling proteins (UCP1–5.
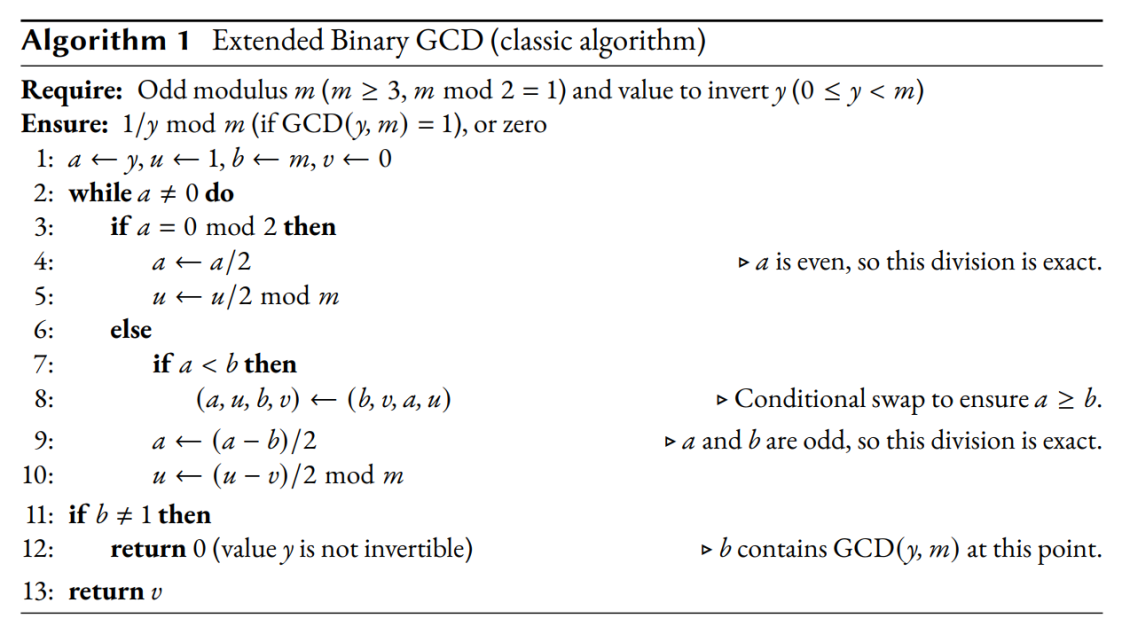
This document describes the OPAQUE protocol, a secure asymmetric passwordauthenticated key exchange (aPAKE) that supports mutual authentication in a clientserver setting without reliance on PKI and with security against precomputation attacks upon server compromise In addition, the protocol provides forward secrecy and the ability to hide the password from the server, even during password. Tl;dr In the context of elliptic curve cryptography To get back from Jacobian coordinates to affine coordinates, you need to compute a multiplicative inverse of a field element, and the binary extended Euclidean algorithm to compute it may leak on side channels A surprising amount of libraries are listed as possibly affected. From A to Z Projective coordinates leakage in the wild Alejandro Cabrera Aldaya and Cesar Pereida García and Billy Bob Brumley Abstract At EUROCRYPT 04, Naccache et al showed that the projective coordinates representation of the resulting point of an elliptic curve scalar multiplication potentially allows to recover some bits of the scalar.
To remove DC leakage using preprocessing 2400, in certain embodiments the encoder side DC leakage is estimated 2410, and then, during the forward POT (eg, 800 at FIG 8), compensation is made for the leakage 23 (before the quantization process) at the encoder The same methods can be used that have already described herein for determining. Amplified when multiplied by the LWE secret s, it is essential to assume that s has small coordinates A major part of our reduction (Section 4) is therefore dedicated to showing a reduction from LWE (in dimension n) with arbitrary secret in Zn q to LWE (in dimension nlog 2 q) with a secret chosen uniformly over f0;1g This. 1 Introduction 11 History and background The subject of control is concerned with methods to manipulate the evolution of dynamical systems As such it is relevant to many fields both inside , , , , , and outside , physics Control has a long history, but it emerged as a modern scientific discipline only after the pioneering work of Norbert Wiener in the 1940s.
Ghost in the Shell Stand Alone Complex A variant appears in the episode "POKER FACE", where a flashback has the Major fire a shot down Saitou's. The set of public keys in CSIDH is a subset of all supersingular elliptic curves defined over F p, in Montgomery form y 2 = x 3 A x 2 x, where A ∈ F p is called the Acoefficient of the curve 1 1 1 Following , we represent A = A ′ / C ′ as a projective point (A ′ C ′);. MethodOur model for pulse propagation in a hollow waveguide is based on paraxial approximation of the NLSE in the following form (see eg, Refs 7 and 8)∇ 2 ⊥ E(r, z, t) − 2 c ∂ 2 ∂z∂t E(r, z, t) = 1 0c 2 ∂ 2 ∂t 2 PNL(r, z, t),(1)where the first and second terms on the lefthand side stand for diffraction and space time.
The damping of propagating waves and loop oscillations is currently a very hot topic, because we are just at the brink of learning which the underlying physical mechanisms are wave leakage (Cally 03;. In appropriate projective coordinates the Hesse pencil is given by the equation (1) λ (x 3 y 3 z 3) μxyz = 0 The pencil was classically known as the syzygetic pencil 2 of cubic curves (see 9, p 230 or 16, p 274), the name attributed to L Cremona. Billy Bob Brumley Tampere University;.
Title From A to Z Projective coordinates leakage in the wild Authors Alejandro Cabrera Aldaya, Cesar Pereida García, Billy Bob Brumley Venue Cryptographic Hardware and Embedded Systems, CHES , Beijing, China, September 1417,. Emergency evacuations are more common than many people realize, including evacuations in the workplace According to the US Department of Homeland Security (DHS) Federal Emergency Management Agency (FEMA), the most frequent causes of evacuations in the US each year are fires and floods In. 813 Likes, 2 Comments UWMilwaukee (@uwmilwaukee) on Instagram “Happy #PantherPrideFriday 🐾💛 us in your photos to be featured on our page or in our Photos of”.
The OceanParcels project develops Parcels (Probably A Really Computationally Efficient Lagrangian Simulator), a set of Python classes and methods to create customisable particle tracking simulations using output from Ocean Circulation modelsParcels can be used to track passive and active particulates such as water, plankton, plastic and fish The code from the OceanParcels project is licensed. In this case the exact WKB analysis leads to consideration of a new sort of Darboux coordinate system on a moduli space of flat \({\mathrm {SL}}(3)\)connections We give the simplest example of such a coordinate system, and verify numerically that in these coordinates the monodromy of the \(T_3\) equation has the expected asymptotic properties. In an episode of Trigun Vash does one better and countersnipes a sniper down the barrel of his own gun — thus destroying the weapon without hurting the sniper Too bad the sniper is a fanatic who promptly pulls out a sidearm and shoots himself;.
Less, LyC escape of galaxies at z ∼ 3 was reported by Iwata et al (09), Nestor et al (11), Mostardi et al (15) and Micheva, Iwata & Inoue (15), but could be suffering from foreground contamination(Sianaetal07;Vanzellaetal10)Sofar,themost convincing cases of LyC leakage in individual galaxies at high red. This family of paraboloids has the formula Ω2 r 2 z = zo = r tan 45°, or z o 3333r 2 − r = 0 for a pressure contour 2g The minimum occurs when dz/dr = 0, or r ≈ 015 m The minimum pressure occurs halfway between points B and C Ans (b) Chapter 2 • Pressure Distribution in a Fluid 141. The vulnerability is in particular present in several recent versions of OpenSSL However, it leaks less than 1 bit of information about the nonce, in the sense that it reveals the most significant bit of the nonce, but with probability.
Projective Coordinates Leak October 03 injecting a fault during the projectivetoaffine conversion process so the erroneous results reveals information about Z (third coordinate of a point. Anthrax is rare in the United States, but outbreaks do occur in wild and domestic animals Yearly vaccination of animals is recommended in areas that have had anthrax in the past The disease is most common in parts of Central and South America, subSaharan Africa, central and southwestern Asia, southern and Eastern Europe, and the Caribbean. Paper From A to Z Projective coordinates leakage in the wild Authors Alejandro Cabrera Aldaya, Tampere University, Tampere, Finland Naccache et al showed that the projective coordinates representation of the resulting point of an elliptic curve scalar multiplication potentially allows to recover some bits of the scalar However, this.
Such access might be granted to an adversary by a poor software implementation that does not erase the Z coordinate of P from the computer’s memory or. 2(α) in Z/2 to be the pushforwards of αvia the two projections to CH n(X)/2 ∼= Z/2 Here is our extension of Karpenko’s theorem 12, Theorem 64 to any characteristic The proof follows the original one but is modified in order to avoid the restriction to smooth quadrics For quasilinear quadrics, the original proof does. Cerebral palsy (CP) is a brain disorder that affects muscle tone and motor skills (the ability to coordinate body movements) A to Z Coxa Valga A to Z Coxa Valga A to Z Failure to Thrive Failure to thrive refers to a child's inability to gain weight and grow as expected for kids of the same age and gender.
Díaz et al 04), resonant absorption (VanDoorsselaere et al 04a;.
From A To Z Projective Coordinates Leakage In The Wild 哔哩哔哩 つロ干杯 Bilibili
Online Template Attacks Springerlink
Online Template Attacks Springerlink
Manuscriptlink Society File S3 Ap Northeast 1 Amazonaws Com Kiisc Wisa Ec 98 A8 Eb 9d Ec 9d B8 Ed 94 84 Eb A1 9c Ec 8b 9c Eb 94 Pdf

Cesar Pereida Garcia S Research Works Tampere University Tampere Uta And Other Places

Cesar Pereida Garcia S Research Works Tampere University Tampere Uta And Other Places
Ninjalab Io Wp Content Uploads 21 01 A Side Journey To Titan Pdf

Same Value Analysis On Edwards Curves Springerlink

Online Template Attacks Springerprofessional De

Pdf From A To Z Projective Coordinates Leakage In The Wild Semantic Scholar
Www Osapublishing Org Optica Viewmedia Cfm Uri Optica 7 10 1232 Seq 0

Alejandro Cabrera Acaldaya Twitter
Ecdsa Side Channel Attack Projective Signatures Ledger Donjon Ctf Writeup Cryptohack Blog
Www Siam Org Meetings Is16 Is16 Abstracts Pdf
Another Paper Accepted At Ches Nisec Tampere Universities
Akiratk0355 Github Io File Slides Wac3 Short Pdf
Alejandro Cabrera Acaldaya Twitter
2
2

Side Channel Analysis And Countermeasure Design On Arm Based Quantum Resistant Sike
Applied Sciences Free Full Text Side Channel Vulnerabilities Of Unified Point Addition On Binary Huff Curve And Its Countermeasure Html
Publications The Cancer Imaging Archive Tcia
Cryptojedi Org Papers Ota Pdf

From A To Z Projective Coordinates Leakage In The Wild Youtube
Akiratk0355 Github Io File Slides Wac3 Short Pdf
Eprint Iacr Org 17 14 Pdf
Akiratk0355 Github Io File Slides Wac3 Short Pdf

Microarchitecture Online Template Attacks Deepai

Abstract 19 Basic Amp Clinical Pharmacology Amp Toxicology Wiley Online Library
Msp Org Obs 4 1 Obs V4 N1 P Pdf
Repository Ubn Ru Nl Bitstream Handle 66 3036 3036 Pdf Sequence 1
Ninjalab Io Wp Content Uploads 21 01 A Side Journey To Titan Pdf
2
2

Side Channel Analysis And Countermeasure Design On Arm Based Quantum Resistant Sike
Ecdsa Side Channel Attack Projective Signatures Ledger Donjon Ctf Writeup Cryptohack Blog
Repository Ubn Ru Nl Bitstream Handle 66 3036 3036 Pdf Sequence 1

Side Channel Analysis And Countermeasure Design On Arm Based Quantum Resistant Sike
Ninjalab Io Wp Content Uploads 21 01 A Side Journey To Titan Pdf
Cryptojedi Org Papers Ota Pdf

Machine Learning For Face Emotion And Pain Recognition
2

From A To Z Projective Coordinates Leakage In The Wild 哔哩哔哩 つロ干杯 Bilibili

User Authentication On Mobile Devices Approaches Threats And Trends Sciencedirect

Alejandro Cabrera Acaldaya Twitter
2

Dip18 2 Hooke Lookbook By School Issuu
Repository Ubn Ru Nl Bitstream Handle 66 3036 3036 Pdf Sequence 1
11th European Headache Federation Congress Jointly With 31st Congress Of The Italian Society For The Study Of Headaches The Journal Of Headache And Pain Full Text

Microarchitecture Online Template Attacks Deepai
2
2

Machine Learning For Face Emotion And Pain Recognition
Eprint Iacr Org 17 669 Pdf

Seminar Archive Colorado College
Repository Ubn Ru Nl Bitstream Handle 66 3036 3036 Pdf Sequence 1
Ls5fqfqjaz0 Gm
Manuscriptlink Society File S3 Ap Northeast 1 Amazonaws Com Kiisc Wisa Ec 98 A8 Eb 9d Ec 9d B8 Ed 94 84 Eb A1 9c Ec 8b 9c Eb 94 Pdf
2

Theory Refinement Implications And Conclusions Emerald Insight
Online Template Attacks Springerlink
Ieeexplore Ieee Org Iel7 Pdf
Repository Ubn Ru Nl Bitstream Handle 66 3036 3036 Pdf Sequence 1

Pdf Microarchitecture Online Template Attacks
Topics Archive Openisme

Seminar Archive Colorado College
2
2
Osa Cavity Quantum Electrodynamics With Color Centers In Diamond
Ieeexplore Ieee Org Iel7 Pdf

Abstract 19 Basic Amp Clinical Pharmacology Amp Toxicology Wiley Online Library
Ieeexplore Ieee Org Iel7 Pdf
2
2
Arxiv Org Pdf 1707 046
Previous Seminars The Faculty Of Mathematics And Computer Science
Applied Sciences Free Full Text Side Channel Vulnerabilities Of Unified Point Addition On Binary Huff Curve And Its Countermeasure Html
Hal Inria Fr Hal Document
Hal Inria Fr Hal Document

Pdf Microarchitecture Online Template Attacks

How To Color Complex Functions Domain Coloring Youtube
Www Ams Org Journals Notices 0511 0511fullissue Pdf

State Of The Environment Of The Black Sea 09 14 5
Ftp Ftp Aoc Nrao Edu Pub Software Aips Text Publ Cookbook Pdf
Cryptojedi Org Papers Ota Pdf

Shared Cortex Cerebellum Dynamics In The Execution And Learning Of A Motor Task Sciencedirect
Cr Yp To Newelliptic Nistecc Pdf
2
Applied Sciences Free Full Text Side Channel Vulnerabilities Of Unified Point Addition On Binary Huff Curve And Its Countermeasure Html
Www Tandfonline Com Doi Pdf 10 1080

Alejandro Cabrera Acaldaya Twitter
2

Microarchitecture Online Template Attacks Deepai

Microarchitecture Online Template Attacks Deepai



